Cryptocurrencies have been dominating news headlines in recent years due to their astronomical value growth. We’ve heard about many people who made small investments in cryptocurrencies, which turned them into millionaires in a short time.

To demonstrate the increased growth of the cryptocurrency market, I have compiled future statistics related to the cryptocurrency market.
- The cryptocurrency market size is expected to grow from USD 1.6 billion in 2021 to USD 2.2 billion by 2026, at a CAGR of 7.1% (globenewswire).
- Bitcoin is expected to reach $100,000 by the end of 2021 (Shervin Pishevar)
- Bitcoin is expected to reach $318,000 by 2022 (Thomas Fitzpatrick)
- There are over 70 million unique cryptocurrency wallets created on Blockchain.com as of May 18, 2021 (Statista)
- Bitcoin had a market capitalization of $1072.21 billion as of February 21st, 2021 (Techjury)
Considering the short time since cryptocurrency was first introduced, the above figures demonstrate that the world’s general direction is moving on to increase the adoption of digital currency.
Cryptocurrencies have become a significant asset in the global economy. The anonymous nature of cryptocurrencies allows hackers to steal them without risking exposing their real identity when trying to trade the stolen currency with cash or other digital assets.
In recent years, cryptocurrency exchange centers have witnessed many security breaches. According to Hackernoon, since 2011, over 60 major cryptocurrency hacks have occurred worldwide, with investors suffering $12.6 billion in losses.
Cryptocurrency exchanges are prime targets for cybercriminals. They hold vast amounts of cash. These centers often lack advanced cybersecurity measures, making them vulnerable.
Stealing money from a crypto exchange system is relatively more straightforward than robbing a traditional bank vault. This makes cryptocurrency exchange platforms suffer from an increased number of sophisticated cyberattacks. In this paper, I will give a general overview of the security implications of running a cryptocurrency exchange center and suggest possible countermeasures to protect both the crypto center and investors from increased cyberattacks.
WHAT IS CRYPTOCURRENCY EXCHANGE CENTER?
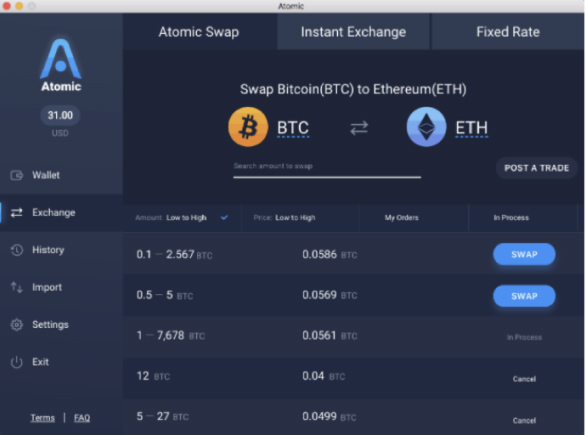
A cryptocurrency exchange, or Digital Currency Exchange (DCU), connects buyers and sellers in one marketplace. For example, users can exchange Bitcoin for USD, Euros, or other digital currencies. These exchanges accept various payment methods, including PayPal, bank transfers, and credit cards, to facilitate trading.
Investing and trading in digital cryptocurrencies can be intimidating at first. However, cryptocurrency exchange platforms exist to simplify and streamline this process. There are numerous cryptocurrency exchange platforms, the following list the most popular providers:
- Coinbase
- Primexbt
- cex
- Changelly
- Poloniex
- Paybis
- Overbit
Before moving on, it is necessary to distinguish between the two cryptocurrency wallet types: Software and hardware wallets.
SOFTWARE WALLET
Also known as the hot wallet (see Figure 1), this wallet is connected to the internet and can be accessed anytime online. Hot wallets are easy to use and can be used to trade various types of cryptocurrencies.
Hot wallet suffer from many disadvantages; for instance, it is more vulnerable to cyberattacks, and could be subject to multiple data protection regulations – For example, if the crypto exchange is offering its services (storing or processing crypto exchange customers’ personal data) to EU citizens, then it must adhere to GDPR and are susceptible to various security vulnerabilities because it is open to the internet.

HARDWARE WALLET
Cold wallets (see Figure 2) are not connected to the internet; hence, they can mitigate all online attacks (phishing, malware, and hacking). The user can receive funds at any time; however, no one can withdraw funds without gaining access to the hardware wallet. The cold wallet is more secure than the hot wallet that could be accessed via the internet.
CYBERATTACKS AGAINST CRYPTOCURRENCY EXCHANGE CENTERS
Cryptocurrency exchange platforms are subject to various cyberattacks.
PHISHING
No matter the type of security defenses already in place, no organization can stop phishing attacks. Phishing is a form of social engineering attack that uses psychological tricks to convince the unaware user to violate the implemented security policies. As with all businesses, Cryptocurrency exchanges are subject to different phishing attacks. In 2020, the US Department of Justice accused two Russian hackers of stealing $16.8m via cryptocurrency phishing sites; the operation started in 2017 and lasted till 2020.
The suspects were running fake websites that allows them to steal digital currencies of hundreds of users registered in the following three cryptocurrency exchange platforms: Poloniex, Binance, and Gemini.
Social engineering attacks against cryptocurrency exchange users are conducted via unsolicited phone calls, SMS messages, and via the internet (phishing emails, messages sent through social media platforms, and internet messaging applications such as WhatsApp).
WEAK SECURITY MEASURES
Crypto exchange providers are not specialized cybersecurity firms. Hence, they are not utilizing the latest defense technology to protect their digital assets. Many outsource their cybersecurity tasks to a third-party provider, which makes them vulnerable to different attacks if the outsourced provider gets hacked.
Another weakness that appears in the security of the cryptocurrency hot wallet is that some crypto exchange platforms secure their users’ hot wallets using a single private key. If an attacker successfully penetrates the system, he can get full access to all stored user’s wallets.
UTILIZING WEAK ACCESS CONTROLS
The security of any IT system is not dependent only on technological defenses. For instance, implementing a weak security authentication system that allows employees to use weak passwords poses a threat. It can open the door for malicious actors to steal stored digital assets.
SECURITY VULNERABILITIES IN CRYPTOCURRENCY EXCHANGE SOFTWARE
A cryptocurrency exchange platform is a software system; it is almost impossible to make a 100% secure IT system. Threat actors try to exploit any vulnerabilities in crypto exchange platforms to steal money and make unauthorized transactions.
Another method used by hackers to steal money from users is distributing fake Android and iOS applications disguised as legitimate trading apps.
DEFENSE STRATEGIES
HOW CAN CRYPTOCURRENCY EXCHANGES ENHANCE THEIR CYBERSECURITY DEFENSES?
Cryptocurrency exchange providers can improve their security defenses and mitigate many types of cyberattacks by doing the following:
- Utilize cyber threat intelligence (CTI) by outsourcing it to a specialized provider. This helps crypto exchanges to gain complete visibility about existing and emerging threats and prevent many attacks before they happen. For example, CTI helps cryptocurrency exchanges discover phishing domain names and criminals groups or hackers planning to launch attacks against them.
- To increase the protection of hot wallets, a crypto exchange provider should utilize Multi-signature Wallets. Under this scheme, there are two or more private keys for each hot wallet that a user needs to use before accessing the wallet or making a transaction.
- Enforce Multi-factor authentication for key employees and Two-factor authentication for other users group. Conduct regular penetration testing exercises against the crypto exchanger platform can save many efforts and money and help providers discover security vulnerabilities in their system before it gets exploited by malicious actors.
- Implementing policies
HOW CAN INVESTORS KEEP THEIR CRYPTO WALLETS SECURE FROM CYBERCRIMINALS?
Ensuring cryptocurrency wallet safety isn’t just the exchange’s responsibility. Users must follow security procedures to protect their funds. Blockchain’s decentralized nature means users have more responsibility for safeguarding their digital assets.
In technical terms, crypto wallets are used to hold users’ digital currency. It is used to store a user private key which is used to authorize online transactions. If cybercriminals succeed in compromising the key, they can –in addition to stealing your money- impersonate user identity to conduct other types of online frauds.
The following suggests best practice security precautions to secure online investor wallets. The following suggests best practice security precautions to secure online investor wallets.
- SAFEGUARD YOUR COMPUTING DEVICE TO SECURE YOUR CRYPT TRANSACTIONS: A good antivirus and antimalware should be installed on an investor computer. Having a personal firewall is also good; most premium antivirus products come with a built-in firewall. However, you can still install a free firewall such as Comodo firewall. Many malware types can record user keystrokes, making them able to steal a user’s crypto private keys.
- KEEP EVERYTHING UP TO DATE: Users’ operating system, installed applications, and all security solutions (Firewall, antivirus, antimalware) must remain up to date to avoid introducing a vulnerability that can lead to a security breach.
- ENCRYPT SENSITIVE DATA: Make sure to utilize encryption to protect your stored digital assets. This effectively prevents cybercriminals from accessing your data, even if they were successful in accessing your system.
- USE A STRONG PASSWORD: Make sure to use a strong password to protect your wallet and other online accounts. To simplify using strong and complex passwords, a user can use a password manager such as KeePass Password Safe to generate complex passwords (see Figure 3) and storing them securely in an encrypted vault.
- PROTECT YOUR MOBILE SYSTEM WITH A PASSWORD: If you are using your mobile devices such as a laptop, tablet, or smartphone to access your online wallet, make sure to protect them using a strong password.
- UTILIZE TWO-FACTOR AUTHENTICATION: If you are using an online wallet, make sure to activate Two-Factor Authentication, so if an adversary gets your crypto account credentials, he still not able to access it.
- USE OFFLINE DIGITAL WALLET STORAGE: This allows you to prevent online attacks against your wallet. For example, you can use a dedicated USB drive to store your offline wallet. Hardware wallets such as those provided by Ledger or Bitlox offer high-security levels as they allow users to isolate their private keys away from their easy-to-hack devices such as laptops or smartphones.
- DISABLE AUTOMATIC LOGINS ON YOUR DEVICE: Making your computer remember your logins is a convenient choice to avoid typing passwords each time you want to access a protected resource. Make sure to disable such features so that no one can access your online wallet if your computing device falls into the wrong hands.
- USE A VPN SERVICE: Make sure to use a VPN service from a trusted provider before accessing your online wallets or conducting any crypto transactions.
- AVOID PHISHING WEBSITES: When connecting to your crypto exchange provider website, make sure you are entering the right website. Cybercriminals try to impersonate legitimate crypto exchange websites to fool unsuspecting users to enter their credentials and steal their crypto accounts.
- USE MULTIPLE WALLETS: As the old wisdom says, do not put all your eggs in one basket. If you have daily transactions and your wallet contain a good amount of money, make sure to use multiple wallets. Put a small amount of money in one hot wallet and dedicate it to your daily transactions while keeping the main amount in one or more cold wallets. It is advisable to use a different password to protect each wallet.
The above security precautions are helpful to secure cryptocurrencies accounts and the end-user devices utilizing them; however, before registering for a specific cryptocurrency exchange account, it is essential for the investor to carefully check the crypto provider offering to make sure it follows the highest security measures in protecting users funds and personal information. Here are some things to consider in your future crypto- exchanger provider.
- What is its insurance policy if a successful hacking attempt or data breach resulted in stealing customers money or other sensitive information?
- Select a cryptocurrency exchange provider that is blockchain-powered. Hence, they keep detailed transaction data.
- What are security defenses implemented by the crypto exchange provider to stop and mitigate cyberattacks?
- Can the crypto exchange employees have access to sensitive client’s data – such as personal information? Always select a provider that can hide customer’s sensitive data even against its employees.
- It is good if the provider is already following known security standards such as the ISO 27002:2013.
- Compliance with relevant data protection regulations such as the GDPR and PCI DSS.
- Check provider website and read previous customers’ reviews about its service. Make sure there are real people behind this provider.
- Consider checking the provider’s privacy policies and terms of service carefully before using its services.
- Finally, make sure the exchange platform is registered under the country where it resides.
COMPLIANCE WITH CRYPTOCURRENCY SECURITY STANDARD (CCSS)
The Cryptocurrency Security Standard (CCSS), introduced in 2014, sets requirements for crypto operations. It standardizes security controls for crypto systems, aiding users in choosing secure platforms. CCSS complements existing standards like ISO 27001:2013 and PCI DSS, focusing on crypto handling. Certification has three levels (1-3), each defining system security controls, with Level 1 being the lowest in CCSS.
SUMMARY
As the cryptocurrency market continues to evolve rapidly, the need to protect people’s investments in this emerging financial system becomes increasingly important. This article shed light on the most prominent cyber threat affecting cryptocurrencies exchange providers and suggest countermeasures to protect users’ cryptocurrencies wallet in both enterprise system and when using personal devices.
FURTHER READING
Best Crypto Exchanges , Accessed 2021-05-21 https://www.investopedia.com/best-crypto-exchanges-5071855
Multisignature Wallets Can Keep Your Coins Safer (If You Use Them Right), Accessed 2021-05-22 https://www.coindesk.com/what-is-a-multisignature-crypto-wallet
CCSS Open Standard Repository, Accessed 2021-05-22
CITATION
Khera, V., 2021. Cryptocurrency Exchange Center: Security Risks, Cyber Defense and Compliance Requirements. [online]Linkedin.com. Available at: [Accessed 30 June 2021].
Contact Cloudsec Asia today to safeguard your organization against cyber threats.
We are your premier cybersecurity solution and consulting provider in the APAC region