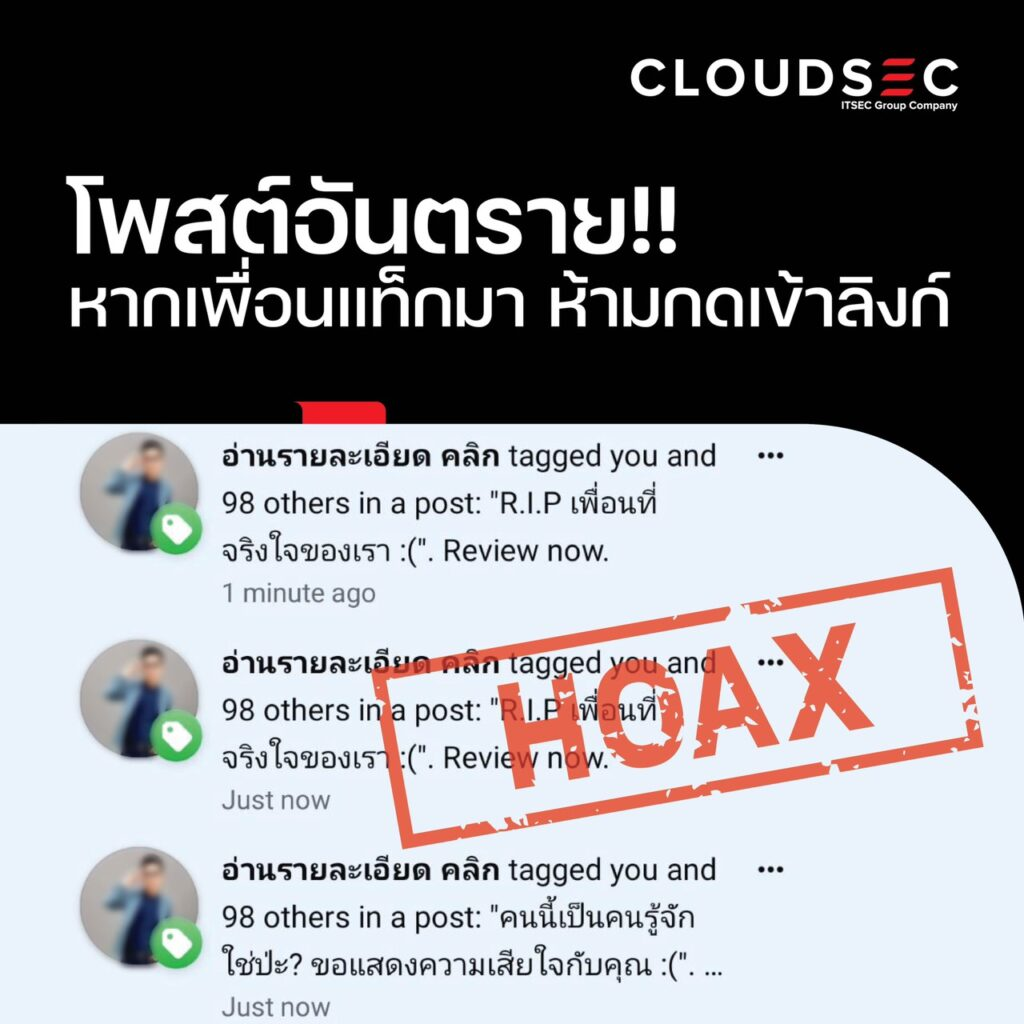
HOAX ภัยร้ายบน Notification Facebook
HOAX คืออะไร การกลับมาระบาดอีกครั้งของมัลแวร์ในคราบของการแท็กโพสต์ทางเฟสบุ๊ก ซึ่งมีรูปแบบเป็นการแท็กเพื่อนคราวละมาก ๆ และมีข้อความในแนวชวนตื่นตระหนก, ข่าวร้าย, หรือเชิญชวนเพื่อหลอกให้คลิกลิงก์ที่คนร้ายได้แนบมา หากมีเหยื่อหลงเชื่อกดลิงก์ดังกล่าวก็จะทำให้บัญชีเฟซบุ๊กของเหยื่ออาจไม่ปลอดภัยอีกต่อไปมัลแวร์ดังกล่าวถูกเรียกว่า Virus Hoax หรือไวรัสข่าวปลอม โดยเมื่อเหยื่อติดไวรัสจากการคลิกลิงก์ไปแล้วก็จะทำให้เหยื่อกลายเป็นผู้กระจายไวรัสนี้ผ่านการแท็กเพื่อน ๆ ในโพสต์ โดยตัวไวรัสมีรูปแบบการทำงานเหมือนกับเว็บฟิชชิ่ง (Phishing) เป็นหน้าล็อกอินเพื่อหลอกให้เหยื่อกรอกอีเมลและรหัสผ่านบัญชี ซึ่งเป็นข้อมูลที่อ่อนไหวของตนลงไป วิธีสังเกตุการคุกคามของ HOAX แบบเบื้องต้น เป็นเพื่อนที่อาจสนิทแต่ไม่ได้มีความเคลื่อนไหวร่วมกันในชีวิตจริง ณ ขณะนั้นแท็กมา

Cyber Security คืออะไร? มาทำความรู้จักให้ลึกซึ้งมากขึ้น
Cyber Security คือ การนำเทคโนโลยี กระบวนการ และแนวทางการปฏิบัติที่ถูกออกแบบโดยเฉพาะมาใช้เพื่อปกป้องเครือข่าย (network Security), อุปกรณ์, โปรแกรม และข้อมูลขององค์กรจากการถูกโจมตีเพื่อสร้างความเสียหาย และเพื่อป้องกันไม่ให้มีการเข้าถึงจากบุคคลที่ไม่ได้รับอนุญาต โดยแนวทางของ Cyber Security มีทั้งหมด 7 อย่าง Network Security การรักษาความปลอดภัยบนเครือข่าย (Network Security) คือ การวางแนวทางการป้องกันการเข้าถึงโครงสร้างพื้นฐานภายในโดยไม่ได้รับอนุญาต
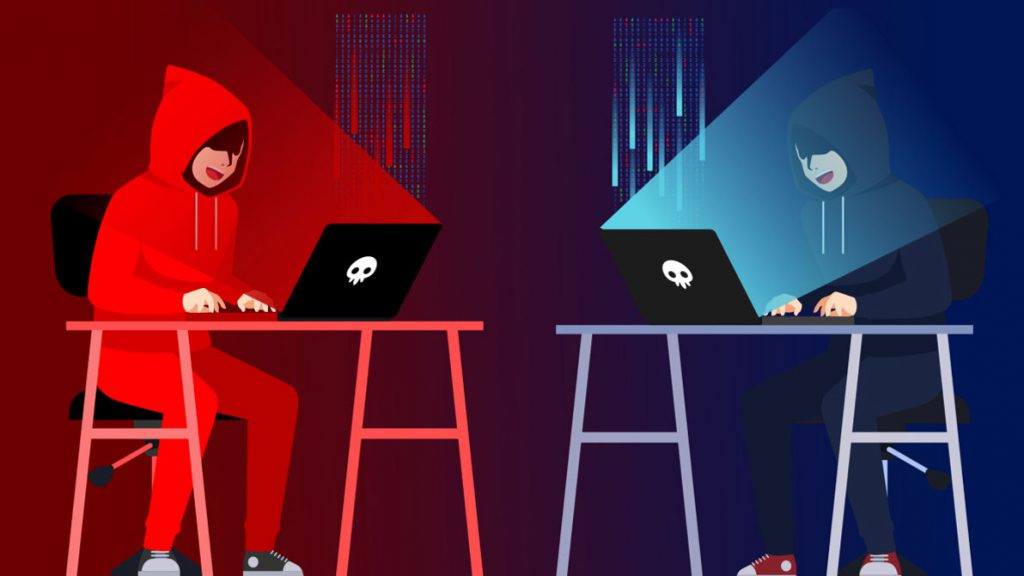
Red Team VS Blue Team
Red Team vs. Blue Team: In the cybersecurity arena, the Red Team and the Blue Team are pivotal in countering cyber threats. This article explores

Tools and Techniques to Investigate the Ownership of Websites
Discover tools & techniques to investigate website ownership. Uncover hidden info behind websites, from domain WHOIS to IP analysis. Websites are designed to show information

Ransomware Attacks: Introduction
As the world continues to digitize, storing data in a digital format becomes a standard across all business sectors. In today’s information age, businesses need

Top 7 Challenges IT Leaders Will Face In 2021
As the digital transformation continues steadily to occupy all our life aspects, the Coronavirus outbreak has speeded the adoption of digital technologies by several years

Social Engineering Attacks: A Practical Introduction
Explore SE Attacks: Psychological cyber-threats via internet, phone & in-person tricks. Learn to prevent breaches. Defend with knowledge.

Cyberattacks Surface and Reduction Strategies
When we talk about cybersecurity defenses, the first thing that comes to our mind is to reduce the cyberattack surface, actually having a small attack

The COVID-19 Effects On Cybersecurity
The COVID-19 pandemic posed challenges for global businesses, shifting work home and necessitating robust COVID-19 cybersecurity. Governments’ restrictions led to a significant remote workforce, highlighting

Cryptocurrency Exchange Center: Security Risks, Cyber Defense and Compliance Requirements
Cryptocurrencies have been dominating news headlines in recent years due to their astronomical value growth. We’ve heard about many people who made small investments in